
Network Security
In today’s hyperconnected world, where data flows seamlessly across networks, the importance of robust network security cannot be overstated. As businesses and individuals alike increasingly rely on digital platforms for communication, transactions, and information storage, the vulnerabilities within these networks become more pronounced. Network security, therefore, emerges as a critical safeguard against cyber threats that can jeopardize sensitive data, disrupt operations, and compromise the integrity of systems. In this comprehensive guide, we delve into the intricacies of network security, exploring key concepts, best practices, and emerging trends to fortify the digital frontier.
Understanding the Landscape:
The landscape of network security is constantly evolving, mirroring the dynamic nature of cyber threats. From sophisticated malware to phishing attacks and ransomware, the arsenal of cybercriminals is expansive. To counteract these threats, organizations must adopt a multi-faceted approach that encompasses various layers of defense.
1. Firewalls: The First Line of Defense
Firewalls serve as the initial barrier between a secure internal network and the vast, potentially hazardous expanse of the internet. These software or hardware-based security mechanisms analyze incoming and outgoing network traffic, permitting or blocking data packets based on predetermined security rules. Effectively configured firewalls act as a first line of defense, preventing unauthorized access and thwarting many common cyber threats.
2. Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): Vigilant Guardians
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) play pivotal roles in detecting and responding to malicious activities within a network. IDS passively monitor network traffic, identifying suspicious patterns or anomalies that may indicate a security breach. On the other hand, IPS take a more proactive stance by actively preventing or blocking unauthorized access and potential threats in real-time. Together, these systems create a vigilant network security posture capable of swift response to emerging risks.
3. Virtual Private Networks (VPNs): Securing Communication Channels
As remote work becomes increasingly prevalent, the need for secure communication channels has never been more critical. Virtual Private Networks (VPNs) encrypt data transmitted between devices, ensuring that even if intercepted, the information remains confidential. By creating a secure tunnel through which data travels, VPNs provide an additional layer of protection, particularly when accessing sensitive information over public networks.
4. Secure Sockets Layer/Transport Layer Security (SSL/TLS): Encrypting Data in Transit
SSL and its successor TLS are cryptographic protocols designed to secure communication over a computer network. These protocols encrypt data in transit, safeguarding it from eavesdropping and tampering. As a fundamental component of secure web browsing, SSL/TLS is instrumental in protecting sensitive information, such as personal details and financial transactions, during online interactions.
5. Endpoint Security: Safeguarding Devices
Endpoints, including computers, mobile devices, and servers, represent potential entry points for cyber threats. Endpoint security solutions encompass a range of measures, from antivirus software to endpoint detection and response (EDR) systems. By fortifying individual devices, organizations can mitigate the risk of malware infections, data breaches, and unauthorized access originating from compromised endpoints.
6. Security Awareness Training: The Human Firewall
While technological solutions form the backbone of network security, the human element remains a critical factor. Cybersecurity awareness training empowers employees to recognize and respond to potential threats, turning them into the first line of defense. By fostering a culture of cybersecurity consciousness, organizations can significantly reduce the likelihood of successful social engineering attacks and insider threats.
In the next section of this guide, we will explore advanced network security strategies, emerging technologies, and the role of artificial intelligence in fortifying digital defenses. Stay tuned as we delve deeper into the ever-evolving realm of network security, equipping you with the knowledge needed to navigate the complex landscape of cyber threats.
Advanced Strategies and Emerging Technologies:
As the threat landscape continues to evolve, network security strategies must adapt to address increasingly sophisticated cyber threats. Advanced strategies and emerging technologies play a pivotal role in staying ahead of malicious actors and fortifying digital defenses.
1. Zero Trust Security Model: Trust No One, Verify Everything
The traditional perimeter-based security model, which assumes that everything within a network is inherently trusted, is becoming obsolete in the face of modern cyber threats. The Zero Trust security model adopts a “never trust, always verify” approach, treating every user, device, and application as potentially untrusted. By implementing strict access controls, continuous monitoring, and multi-factor authentication, organizations can minimize the risk of unauthorized access and lateral movement within their networks.
2. Network Segmentation: Containing Threats
Network segmentation involves dividing a network into smaller, isolated segments to contain the spread of a potential security breach. By restricting lateral movement, even if a threat infiltrates one segment, its impact can be limited. Properly implemented network segmentation enhances security by creating barriers that prevent attackers from moving freely throughout the network, providing organizations with better control and visibility.
3. Advanced Persistent Threat (APT) Protection: Long-Term Defense
Advanced Persistent Threats (APTs) are sophisticated, targeted attacks that often go undetected for extended periods. APT protection involves a holistic approach that combines advanced threat detection, continuous monitoring, and incident response capabilities. Machine learning and behavioral analytics are crucial components of APT protection, enabling the identification of subtle anomalies indicative of a persistent and stealthy threat.
4. Next-Generation Firewalls: Beyond the Basics
Next-Generation Firewalls (NGFWs) go beyond traditional firewalls by incorporating advanced features such as intrusion prevention, application awareness, and deep packet inspection. These capabilities enable NGFWs to provide more granular control over network traffic and detect and block sophisticated threats. NGFWs are essential for safeguarding networks against evolving cyber threats, especially as applications and attack methods become more sophisticated.
5. Security Information and Event Management (SIEM): Centralized Intelligence
SIEM solutions collect and analyze log data from various network devices, applications, and systems in real-time. By correlating and aggregating this information, SIEM systems provide a centralized view of an organization’s security posture. This centralized intelligence helps identify and respond to security incidents promptly, facilitating compliance with regulatory requirements and enhancing overall situational awareness.
6. Artificial Intelligence (AI) and Machine Learning (ML): Augmenting Security Defenses
AI and ML technologies have become integral components of advanced network security. These technologies enhance threat detection, automate incident response, and provide predictive analysis to identify potential vulnerabilities. AI and ML algorithms can analyze vast amounts of data at speeds impossible for humans, enabling organizations to stay ahead of rapidly evolving threats and detect patterns indicative of malicious activity.
7. Blockchain Technology: Immutable Security
While blockchain is widely known for its applications in cryptocurrencies, its underlying principles of decentralization and immutability can be leveraged for enhancing network security. Blockchain can be used to secure transactions, establish identity verification systems, and create tamper-resistant logs. As a decentralized and transparent technology, blockchain adds an additional layer of trust to digital interactions.
Incident Response and Business Continuity: Navigating the Aftermath
No network security strategy is foolproof, and organizations must prepare for the inevitability of security incidents. An effective incident response plan coupled with a robust business continuity strategy is essential to minimize the impact of security breaches, maintain operations, and safeguard the integrity of critical assets.
1. Incident Response Plan: A Blueprint for Action
An incident response plan is a structured approach outlining the steps an organization will take in the event of a security incident. The plan typically includes identification, containment, eradication, recovery, and lessons learned phases. Rapid detection and containment are crucial to limiting the damage caused by a security incident. Organizations should regularly test and update their incident response plans to ensure effectiveness in the face of evolving threats.
2. Cybersecurity Incident Response Team (CIRT): A Coordinated Effort
A Cybersecurity Incident Response Team (CIRT) is a dedicated group of professionals responsible for implementing the incident response plan. This team, comprising individuals with expertise in forensics, network security, legal matters, and communication, plays a pivotal role in orchestrating a coordinated response to security incidents. Effective communication and collaboration are essential to ensure a swift and efficient resolution.
3. Digital Forensics: Unraveling the Intricacies
Digital forensics involves the collection, analysis, and preservation of electronic evidence to investigate and reconstruct security incidents. This process helps identify the root cause of an incident, trace the extent of the compromise, and gather information for legal proceedings if necessary. Leveraging digital forensics capabilities enhances an organization’s ability to learn from incidents and strengthen its security posture.
4. Business Continuity and Disaster Recovery: Ensuring Resilience
While incident response focuses on addressing the immediate aftermath of a security incident, business continuity and disaster recovery planning extend the scope to maintaining essential business functions and services. Organizations should develop comprehensive strategies for data backup, system recovery, and alternative operational procedures to ensure continuity in the face of disruptions. Regular testing and updating of these plans are essential to guarantee their effectiveness.
5. Cyber Insurance: Mitigating Financial Impact
As the financial ramifications of cyber incidents can be substantial, many organizations are turning to cyber insurance to mitigate the associated costs. Cyber insurance policies can cover a range of expenses, including legal fees, notification costs, and loss of revenue. However, it’s crucial for organizations to carefully review and understand the terms of their policies, ensuring they align with their specific risk profile and security measures.
6. Regulatory Compliance: Navigating Legal Obligations
Various industries are subject to specific regulatory frameworks mandating data protection and cybersecurity standards. Compliance with these regulations is not only essential for legal reasons but also contributes to the overall security posture of an organization. Regular audits and assessments can help ensure that security measures align with regulatory requirements, reducing the risk of penalties and legal consequences.
7. Continuous Monitoring and Learning: Adapting to Evolving Threats
The landscape of cyber threats is in constant flux, necessitating a continuous learning and adaptation cycle. Organizations should establish mechanisms for continuous monitoring of their network security posture, staying informed about emerging threats, and updating security measures accordingly. Learning from past incidents and incorporating those lessons into future security strategies is crucial for building resilience against evolving cyber threats.
Conclusion:
In the ever-evolving landscape of network security, organizations must adopt a proactive and adaptive mindset to stay ahead of cyber threats. The combination of robust foundational measures, advanced strategies, and emerging technologies creates a comprehensive defense framework that can withstand the complexities of the digital frontier.
As we conclude this segment of our guide, we’ve explored the fundamental elements of network security, from firewalls and encryption to advanced strategies like Zero Trust and emerging technologies such as AI and blockchain. In the next section, we will turn our attention to the crucial aspect of incident response and recovery, examining how organizations can effectively mitigate the impact of security incidents and ensure business continuity in the face of cyber threats. Stay with us as we continue our journey into the depths of network security, unraveling the strategies that form the backbone of a resilient and secure digital infrastructure.
As we conclude our exploration of network security, it becomes evident that building a resilient network security ecosystem requires a holistic and proactive approach. From foundational measures and advanced strategies to incident response and business continuity planning, each element plays a crucial role in safeguarding the digital frontier.
In the fast-paced world of cybersecurity, staying one step ahead of cyber threats is an ongoing challenge. By integrating the principles and practices discussed in this guide, organizations can establish a robust defense against a diverse array of threats. As technology evolves, so too must our approach to network security. Regular assessments, updates, and a commitment to a culture of security awareness are fundamental to maintaining a strong and adaptable defense against the ever-changing landscape of cyber threats.
Stay vigilant, stay informed, and embrace the dynamic nature of network security as you navigate the digital realm. Together, we can fortify the digital frontier and ensure a secure and resilient future for the interconnected world.
admin
Related Posts
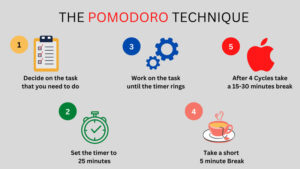
The Pomodoro Technique: Boosting Productivity and Focus
In the quest for enhanced productivity and improved focus, the Pomodoro Technique stands as a beacon of efficiency. This time management method, developed by Francesco
Riding the Cloud: Unraveling the Boom in Cloud Computing
Cloud computing has revolutionized the way we work, communicate, and store data. It is a technology that has been around for over a decade, but
Unleashing Power BI’s Potential: Converting Data into Knowledge
Unleashing Power BI’s Potential: Converting Data into Knowledge Businesses continuously struggle to harness massive amounts of data in today’s data-driven environment in order to make


